Cisco ASDM Launcher fails with latest Java 8+
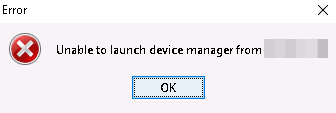
You have a Cisco ASDM launcher and your launcher does not start anymore with JRE 7, JRE 8, JRE 9, JRE 10, JRE 11, JRE 12+. You get the error:
Probably this issue came from an Java Update.
Table of Contents
1. Identify the error
To identify which error you have, you need to open the java console
If you find something similar to this error (exception), your java security configuration is the issue of this error:
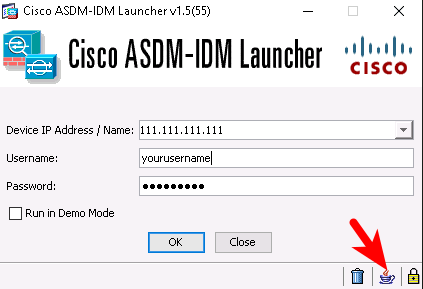
Local Launcher Version = 1.5.55
Local Launcher Version Display = 1.5(55)
OK button clicked
Trying for ASDM Version file; url = https://111.111.111.111/admin/
javax.net.ssl.SSLHandshakeException: Received fatal alert: handshake_failure
at sun.security.ssl.Alerts.getSSLException(Unknown Source)
at sun.security.ssl.Alerts.getSSLException(Unknown Source)
at sun.security.ssl.SSLSocketImpl.recvAlert(Unknown Source)
at sun.security.ssl.SSLSocketImpl.readRecord(Unknown Source)
at sun.security.ssl.SSLSocketImpl.performInitialHandshake(Unknown Source)
at sun.security.ssl.SSLSocketImpl.startHandshake(Unknown Source)
at sun.security.ssl.SSLSocketImpl.startHandshake(Unknown Source)
at sun.net.www.protocol.https.HttpsClient.afterConnect(Unknown Source)
at sun.net.www.protocol.https.AbstractDelegateHttpsURLConnection.connect(Unknown Source)
at sun.net.www.protocol.https.HttpsURLConnectionImpl.connect(Unknown Source)
at com.cisco.launcher.y.a(Unknown Source)
at com.cisco.launcher.y.if(Unknown Source)
at com.cisco.launcher.r.a(Unknown Source)
at com.cisco.launcher.s.do(Unknown Source)
at com.cisco.launcher.s.null(Unknown Source)
at com.cisco.launcher.s.new(Unknown Source)
at com.cisco.launcher.s.access$000(Unknown Source)
at com.cisco.launcher.s$2.a(Unknown Source)
at com.cisco.launcher.g$2.run(Unknown Source)
at java.lang.Thread.run(Unknown Source)
Trying for IDM. url=https://111.111.111.111/idm/idm.jnlp/
javax.net.ssl.SSLHandshakeException: Received fatal alert: handshake_failure
at sun.security.ssl.Alerts.getSSLException(Unknown Source)
at sun.security.ssl.Alerts.getSSLException(Unknown Source)
at sun.security.ssl.SSLSocketImpl.recvAlert(Unknown Source)
at sun.security.ssl.SSLSocketImpl.readRecord(Unknown Source)
at sun.security.ssl.SSLSocketImpl.performInitialHandshake(Unknown Source)
at sun.security.ssl.SSLSocketImpl.startHandshake(Unknown Source)
at sun.security.ssl.SSLSocketImpl.startHandshake(Unknown Source)
at sun.net.www.protocol.https.HttpsClient.afterConnect(Unknown Source)
at sun.net.www.protocol.https.AbstractDelegateHttpsURLConnection.connect(Unknown Source)
at sun.net.www.protocol.http.HttpURLConnection.getInputStream0(Unknown Source)
at sun.net.www.protocol.http.HttpURLConnection.getInputStream(Unknown Source)
at sun.net.www.protocol.https.HttpsURLConnectionImpl.getInputStream(Unknown Source)
at com.cisco.launcher.w.a(Unknown Source)
at com.cisco.launcher.s.for(Unknown Source)
at com.cisco.launcher.s.new(Unknown Source)
at com.cisco.launcher.s.access$000(Unknown Source)
at com.cisco.launcher.s$2.a(Unknown Source)
at com.cisco.launcher.g$2.run(Unknown Source)
at java.lang.Thread.run(Unknown Source)
2. What is the root cause?
Oracle has disabled any well known unsafe and unsecure cipher and algorithm. You can re-enable this again, but sadly you have to enable it fully for the complete installation of Java. This means you have to enable unsecure protocols for any java application. Typically it is no issue, but could be in some security relevant environments.
3. How to fix it?
Best way would be to upgrade your Firewall to later Software version. Sometimes this is not possible. In this case you have to stick to the outdated Cisco Software, and you have to find a solution locally in Java.
3.1. Modify the existing JRE for your Cisco ASDM
find out your active java version by typing in your command line
java -version
Now go to your JRE version specific folder, which is typically under
Windows: C:\Program Files\Java\jre
Ubuntu: /usr/lib/jvm/
Find the file
java.security
and open it in your prefered editor (open the editor as administrator or with sudo)
Now find the section which contains this:
jdk.tls.disabledAlgorithms=SSLv3, RC4, DES, MD5withRSA, DH keySize < 1024, \
EC keySize < 224, 3DES_EDE_CBC, anon, NULL
and change it to
#jdk.tls.disabledAlgorithms=SSLv3, RC4, DES, MD5withRSA, DH keySize < 1024, \
# EC keySize < 224, 3DES_EDE_CBC, anon, NULL
jdk.tls.disabledAlgorithms=SSLv3, RC4, DES, MD5withRSA, DH keySize < 1024, \
EC keySize < 224, anon, NULL
restart your ASDM and the issue shall be gone
If the issue still persists connect with your browser to the ASDM (https://<yourFirewall>) in the above example it was
https://111.111.111.111
and open in the Browser the SSL details of your connection
<screenshot>
3.2. Prepare a dedicated JRE only for Cisco ASDM (hard way, but more secure)
In this variant you clone a JRE to a different folder and you only use this JRE for the ASDM. This is the most secure way for all other application, since you limit the bad unsecure protocols to Cisco ASDM only.
To achieve this, copy your existing JRE to a special location, and create a script which sets JAVA_HOME and PATH to run java from this new folder.
<to be written>


